Free Shiping
On most orders
Bitcoin Accepted
On most orders
Support 24/7
Online 24 hours
100% Safe
Secure shopping
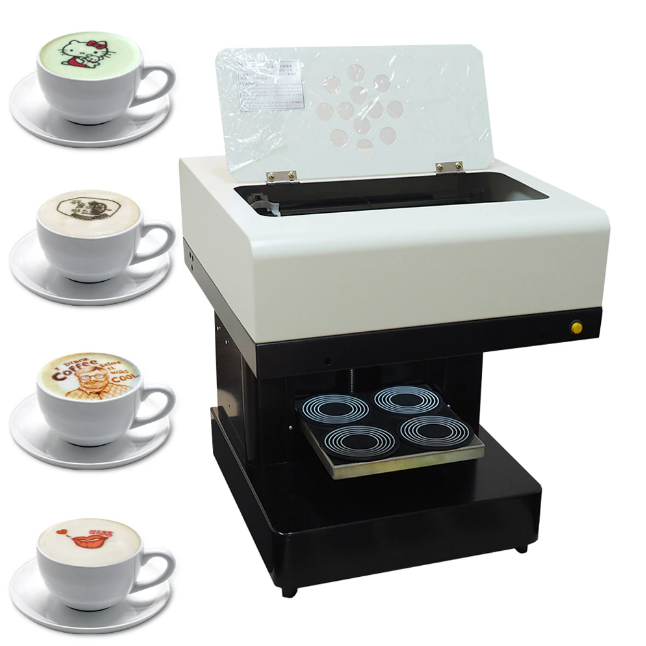
Barista
Mini Express Lichtenstein
Portable Electric Espresso Machine
Nespresso Vertuo Espresso Machine
Breville BES870XL Espresso Machine
PHILIPS 3200 Espresso Machine
Automatic Espresso Machine by Affetto
Classic Stovetop Espresso Maker
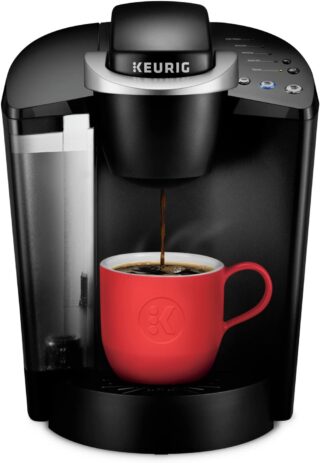
Keurig K-Classic Coffee Maker
Featured
Our Shop
Double Wall Glasses Coffee Cups
Toilet Poop Stool Squatty Potty
Rated 4.75 out of 5 based on 4 customer ratings
Jump Starter 2000A Peak Portable Battery
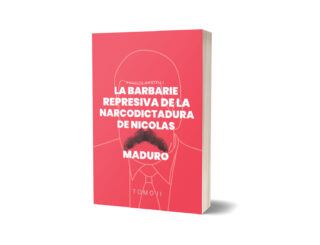
La Barbarie Represiva de la Narcodictadura de Nicolás Maduro II
Canon EOS 2000D Rebel T7 DSLR Camera
Biblioteca
La Barbarie Represiva de la Narcodictadura de Nicolás Maduro II$28.99 Original price was: $28.99.$23.99Current price is: $23.99.
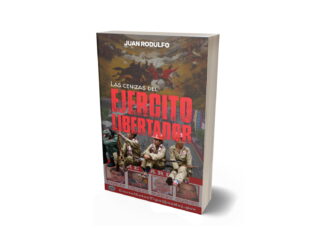
Las cenizas del Ejército Libertador$47.00 Original price was: $47.00.$32.99Current price is: $32.99.
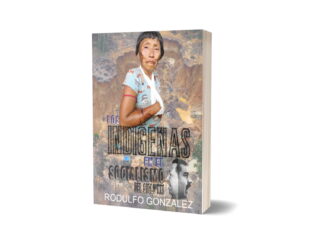
Los Indígenas en el Socialismo del Siglo XXI$32.99 Original price was: $32.99.$27.99Current price is: $27.99.
Política explicada para Millennials: Gens XYZ y próximas generaciones$28.99 Original price was: $28.99.$17.99Current price is: $17.99.
La Hemeroteca Loca VI$8.99 Original price was: $8.99.$6.99Current price is: $6.99.
La Hemeroteca Loca V$7.99 Original price was: $7.99.$5.99Current price is: $5.99.
La Hemeroteca Loca IV$14.99 Original price was: $14.99.$9.99Current price is: $9.99.
Historia de los Primeros Periódicos de América Latina$12.00 Original price was: $12.00.$9.78Current price is: $9.78.
Entre Sueños$9.88 Original price was: $9.88.$7.89Current price is: $7.89.
Morir en el Socialismo del Siglo XXI: Tomo V$25.99 Original price was: $25.99.$17.99Current price is: $17.99.
Morir en el Socialismo del Siglo XXI: Tomo IV$25.99 Original price was: $25.99.$19.99Current price is: $19.99.
Morir en el Socialismo del Siglo XXI Tomo III$17.99 Original price was: $17.99.$10.73Current price is: $10.73.
Morir en el Socialismo del Siglo XXI Tomo I$25.99 Original price was: $25.99.$17.99Current price is: $17.99.
Grandes Intérpretes del Bolero$57.80 Original price was: $57.80.$48.99Current price is: $48.99.
Colección La Guerra del Dictador Hugo Chavez: Contra Comunicadores Sociales y Medios$84.00 Original price was: $84.00.$68.50Current price is: $68.50.
Morir en el Socialismo del Siglo XXI: Tomo II$28.99 Original price was: $28.99.$13.99Current price is: $13.99.
El Asesinato del Capitán de Corbeta Rafael Acosta Arévalo$28.99 Original price was: $28.99.$17.99Current price is: $17.99.
La Guerra del dictador Hugo Chavez contra los Medios en el 2007$13.99 Original price was: $13.99.$10.50Current price is: $10.50.
Noche y Otros Poemas Breves$9.40 Original price was: $9.40.$7.77Current price is: $7.77.
El Asesinato de Fernando Alban$28.99 Original price was: $28.99.$17.99Current price is: $17.99.